Web Penetration Testing - Access Control

Building a Resilient Infrastructure with NIST SP 800-171 Guidelines
August 3, 2023
Best Practices for Secure File Uploads in Web Applications
August 1, 2023
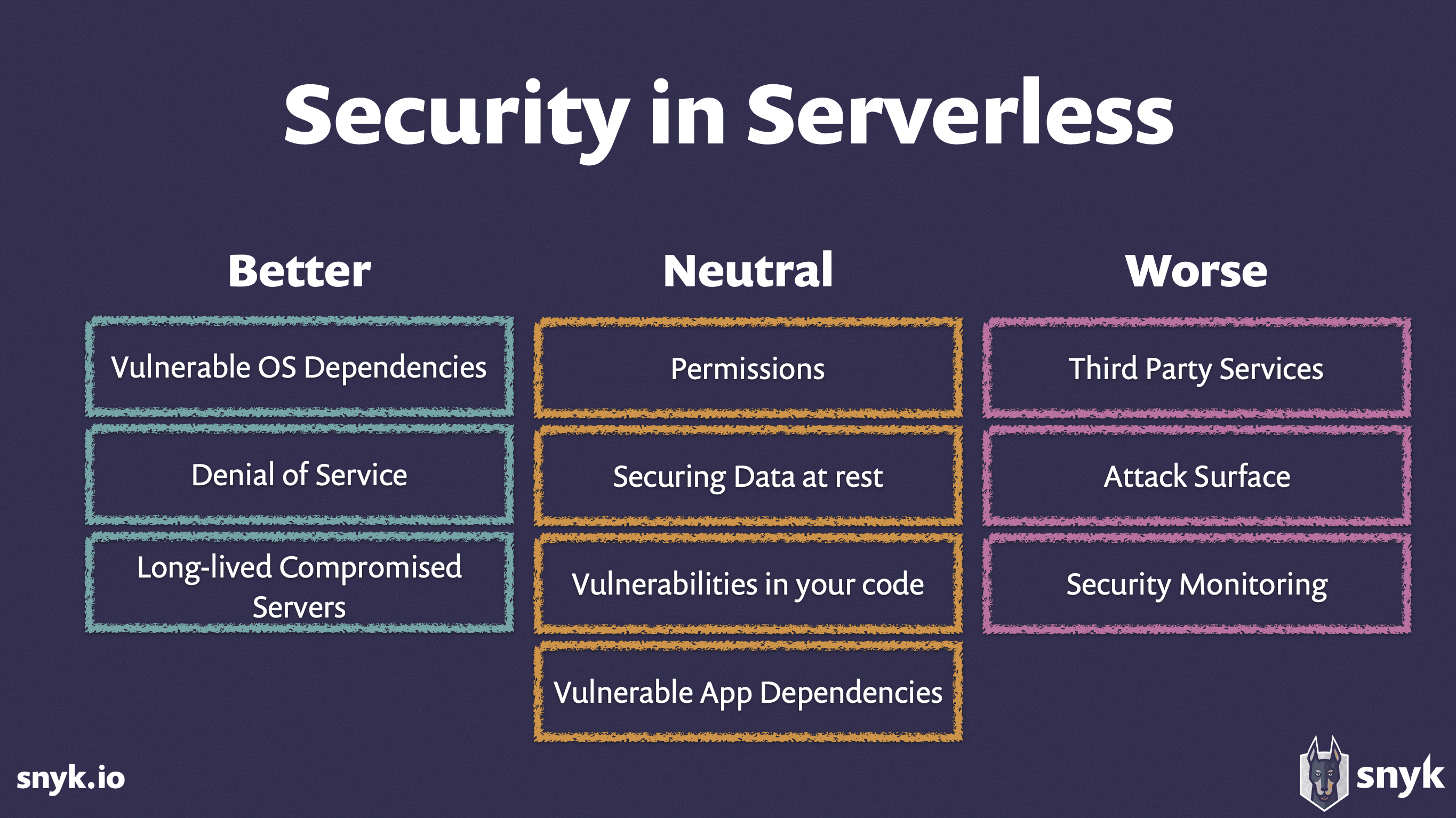
Security Challenges in Serverless Architectures: Web Applications
August 1, 2023
Server-Side Request Manipulation: Exploitation Techniques
July 16, 2023

GraphQL Security: Common Vulnerabilities and Best Practices
July 25, 2023
Business Logic Flaws in Web Applications: Detection and Exploitation
July 24, 2023

OAuth Security: Risks and Recommendations for Web Developers
July 19, 2023
Insecure Direct Object References (IDOR): Exploitation and Prevention
July 17, 2023

Social Engineering Tactics and Their Impact on Security Vulnerabilities
May 13, 2023

How to Protect Your Data in the Cloud
June 26, 2023