Web Penetration Testing - Code Review

Assessing Third-Party Web Application Security Risks
July 28, 2023
Business Logic Flaws in Web Applications: Detection and Exploitation
July 24, 2023
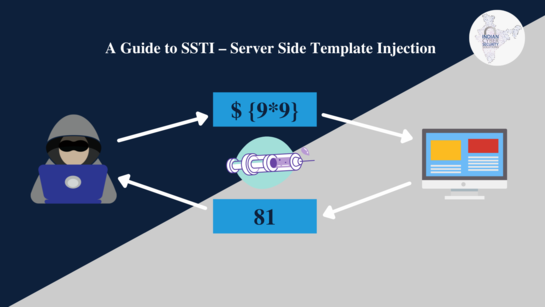
Server-Side Template Injection (SSTI): Exploitation Techniques
July 15, 2023

Understanding Different Web Application Security Testing Techniques
June 5, 2023

What Priority Is Looking For Security Vulnerabilities In The Packages And Libraries?
June 3, 2023