Web Penetration Testing - Communication

WebSocket Hijacking: Techniques and Countermeasures
July 31, 2023
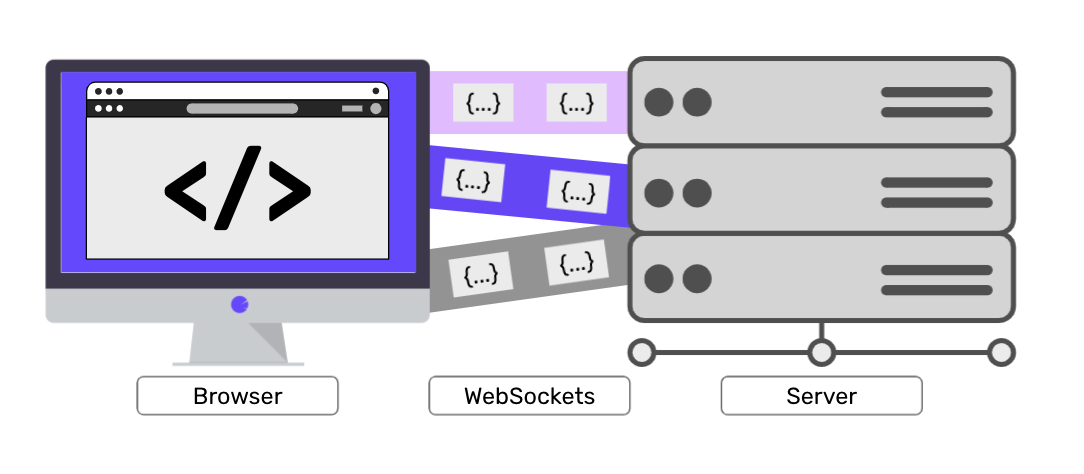
Websockets Security: Threats and Countermeasures
July 20, 2023
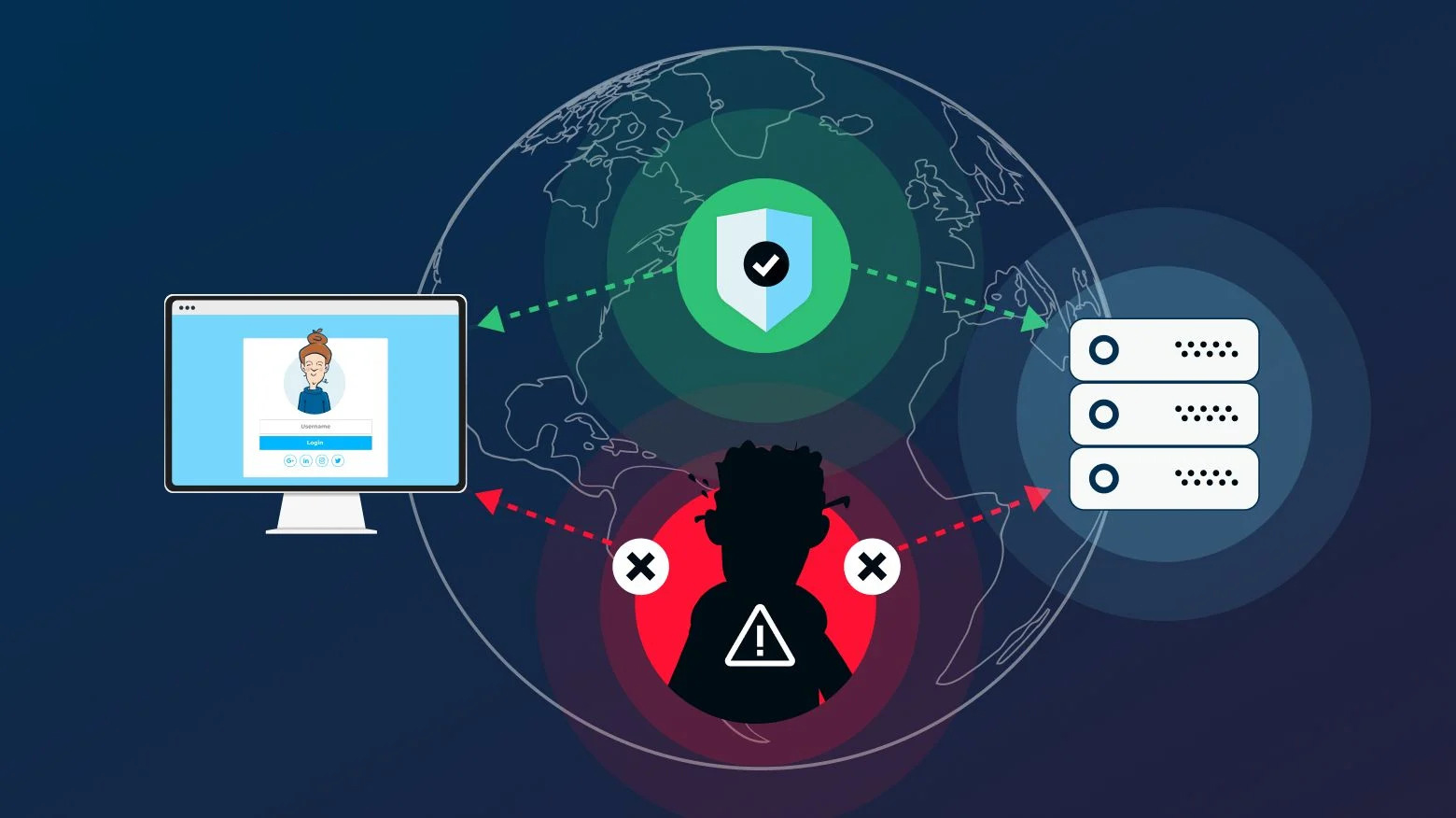
Man-in-the-Middle (MitM) Attacks on Web Applications
July 18, 2023

Penetration Testing and Reporting Results Effectively
May 12, 2023
Power of Encryption in Safeguarding Your Digital World
May 17, 2023

How to Develop a Cybersecurity Incident Response Plan for Your Business
May 6, 2023
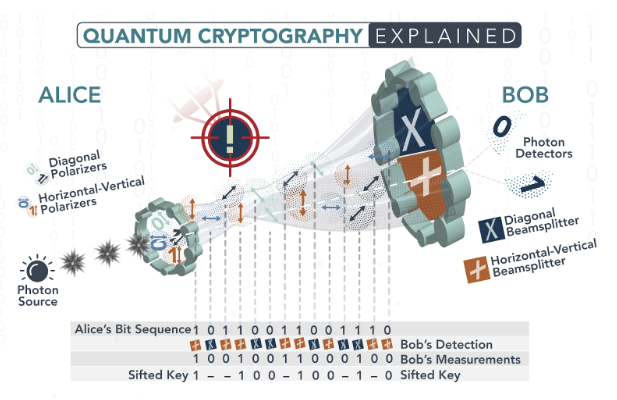
Exploring Quantum Cryptography: The Future of Unbreakable Encryption
June 14, 2023