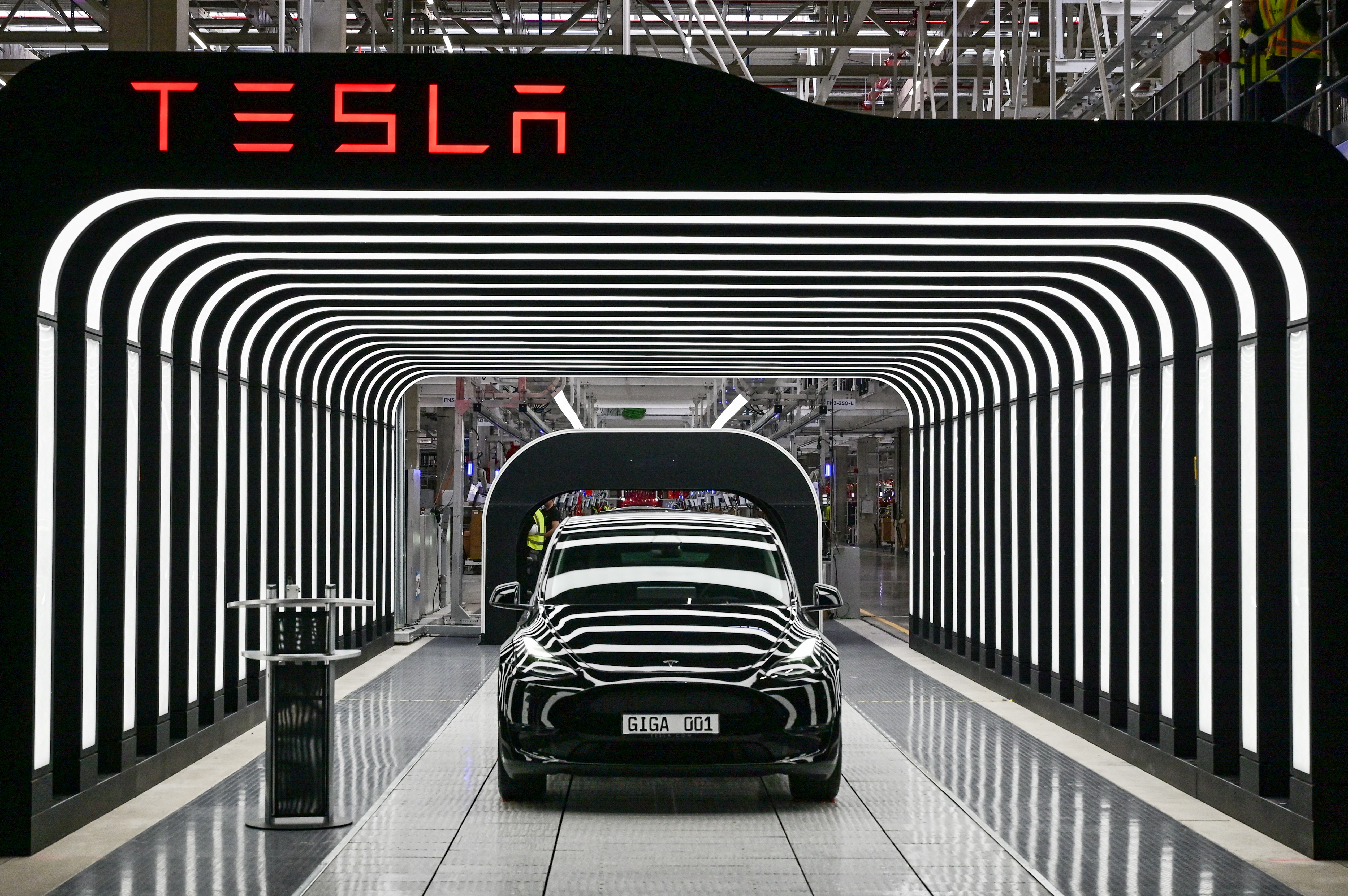
Massive Tesla Leak Reveals Data Breaches, Thousands of Safety Complaints
May 29, 2023

The Importance of Data Privacy Regulations: GDPR, CCPA, and Their Impact
June 20, 2023

How to Protect Your Data in the Cloud
June 26, 2023
What Technique is Used To Automate The Detection Of Web Application Vulnerabilities
May 30, 2023

Securing Cloud-Native Applications: Considerations and Best Practices
June 13, 2023