Web Penetration Testing - Encryption
HIPAA and Cloud Computing: Security Considerations for CISOs
August 2, 2023
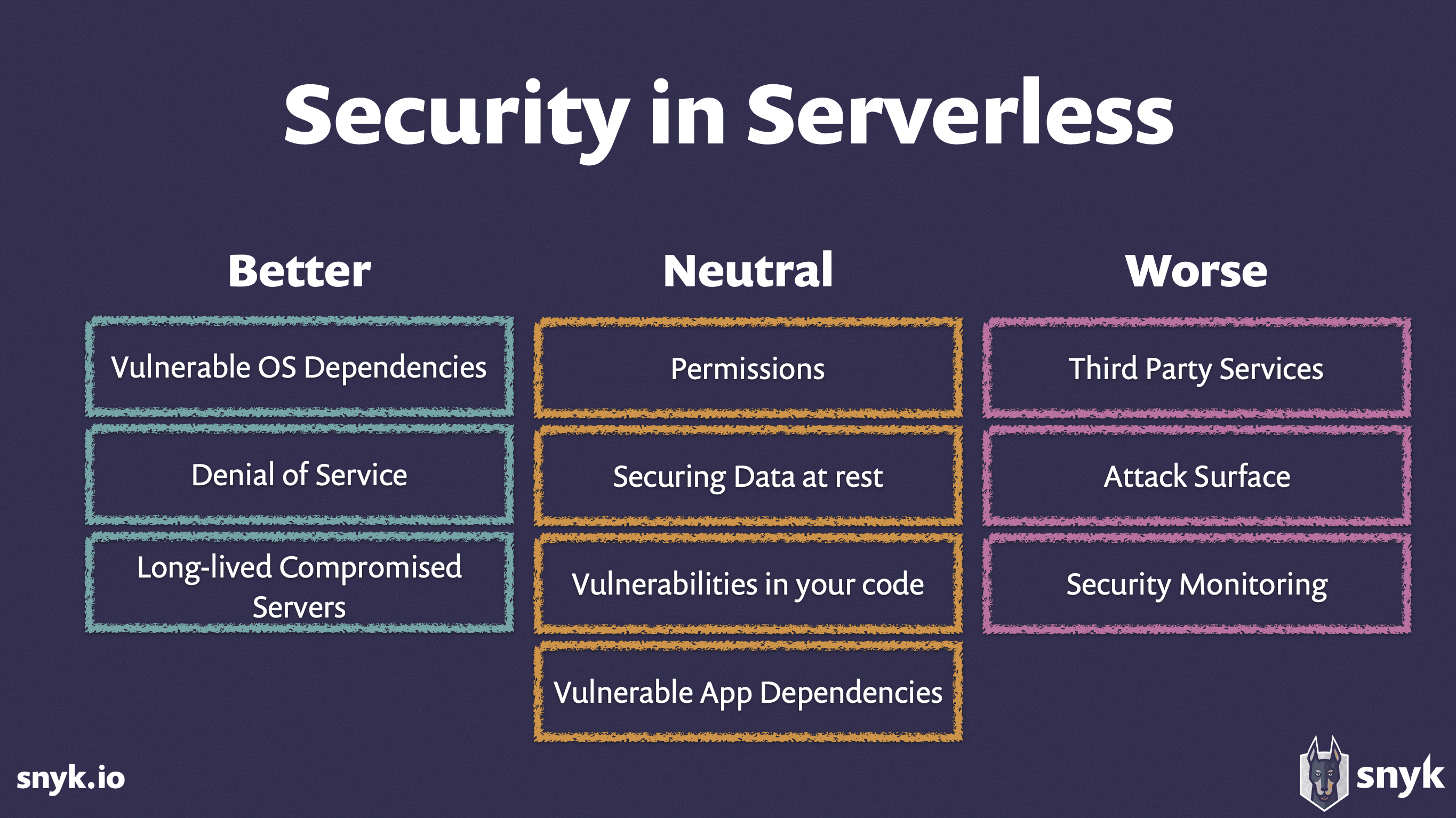
Security Challenges in Serverless Architectures: Web Applications
August 1, 2023
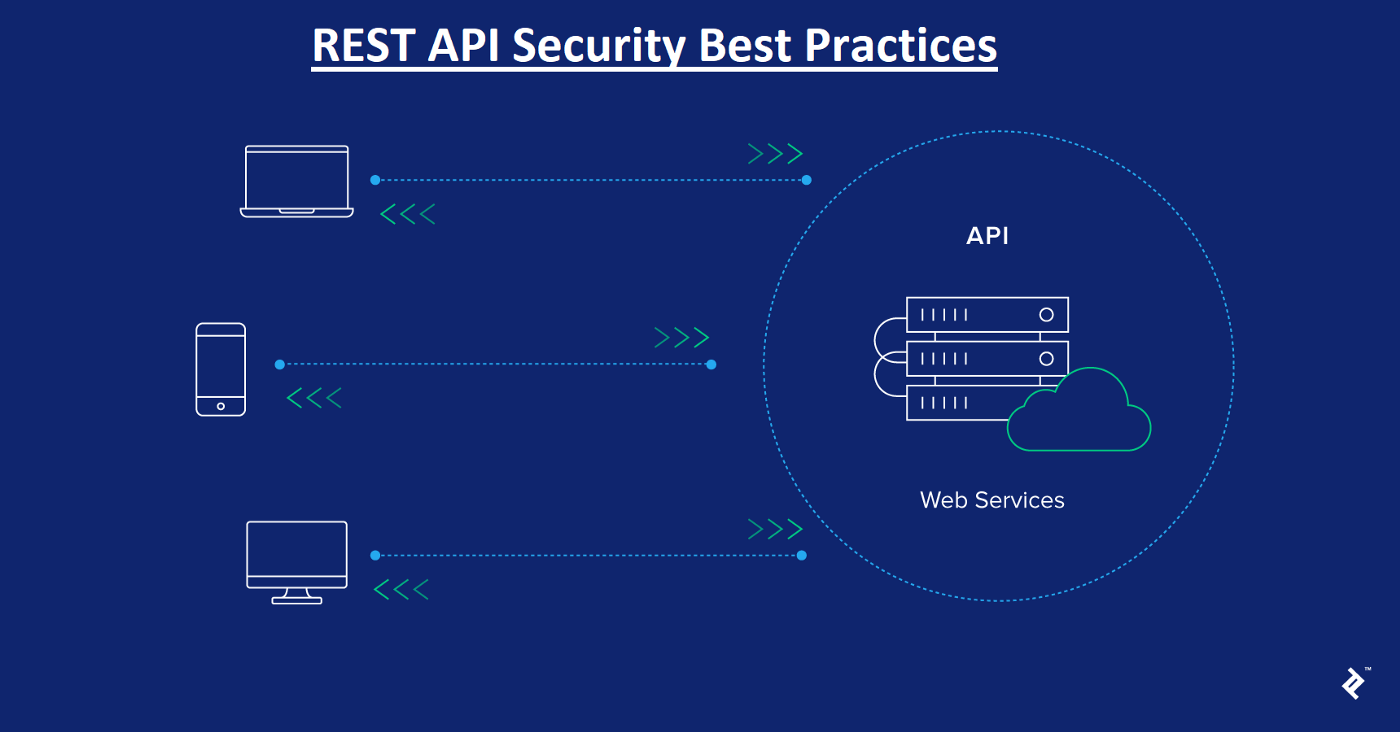
Security Considerations for RESTful Web Services
July 31, 2023
Server-Side Request Manipulation: Exploitation Techniques
July 16, 2023
Importance of Secure Session Management in Web Applications
July 22, 2023
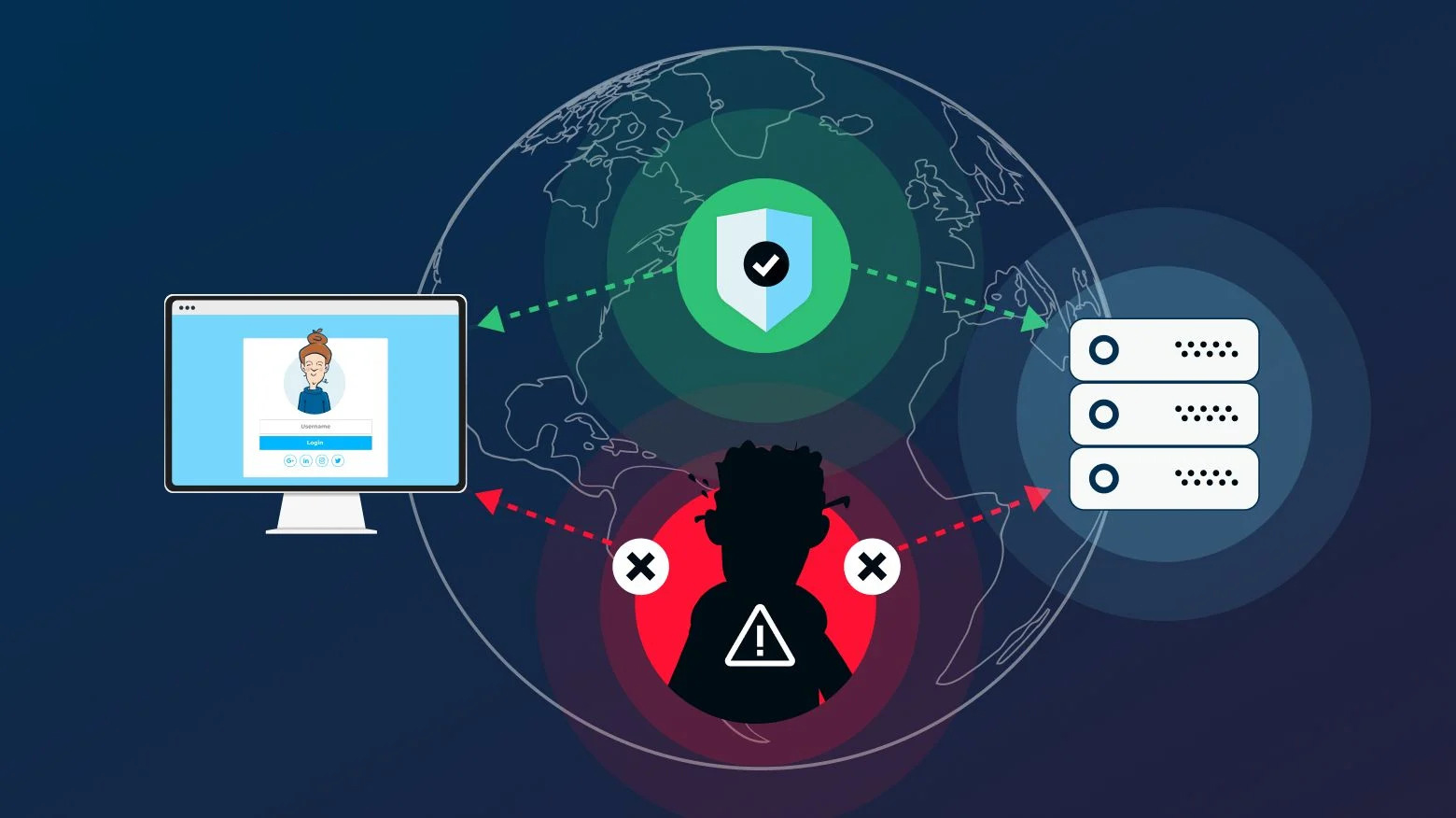
Man-in-the-Middle (MitM) Attacks on Web Applications
July 18, 2023
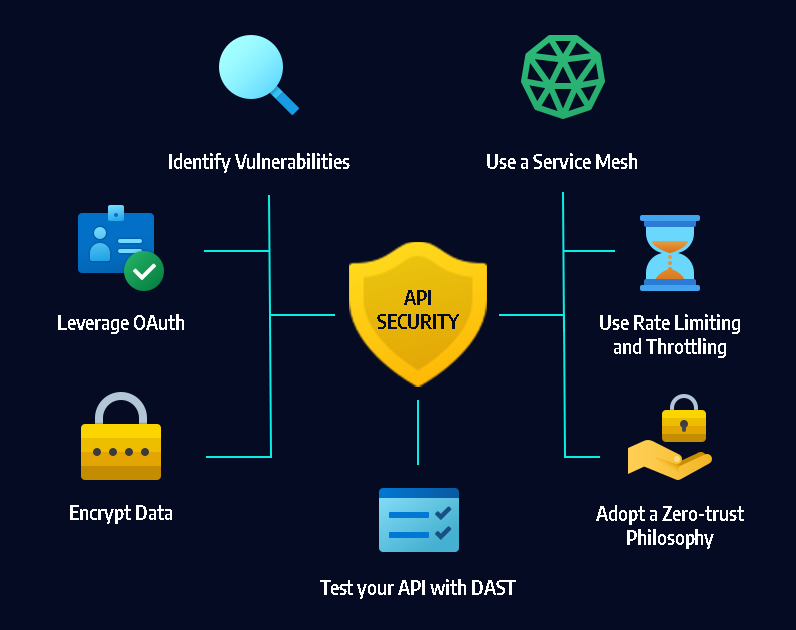
API Security Testing: Best Practices and Tools
July 12, 2023
Ransomware Detection Techniques Using Machine Learning
May 12, 2023

Protecting Your Wireless Network Against Cyber Attacks
May 12, 2023
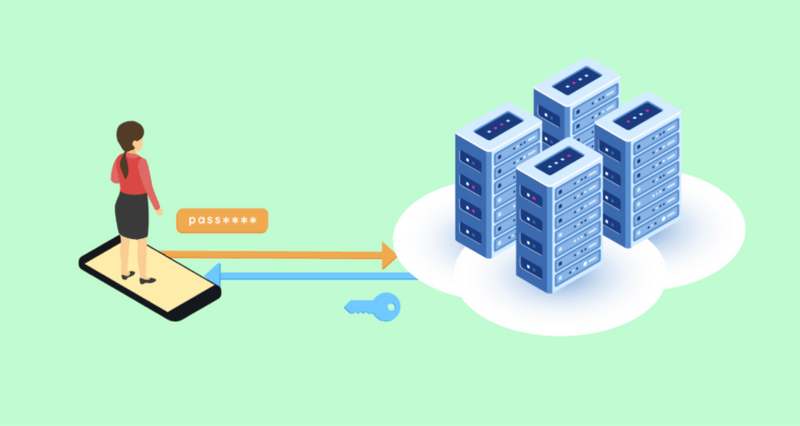
Power of Encryption in Safeguarding Your Digital World
May 17, 2023
Understanding Ransomware through Reverse Engineering
May 11, 2023

The Future of Ransomware
May 11, 2023

Understanding The Dark Web And Its Role In Cybercrime
May 9, 2023

How to Protect Your Data in the Cloud
June 26, 2023

The Best Password Managers for 2023
June 23, 2023
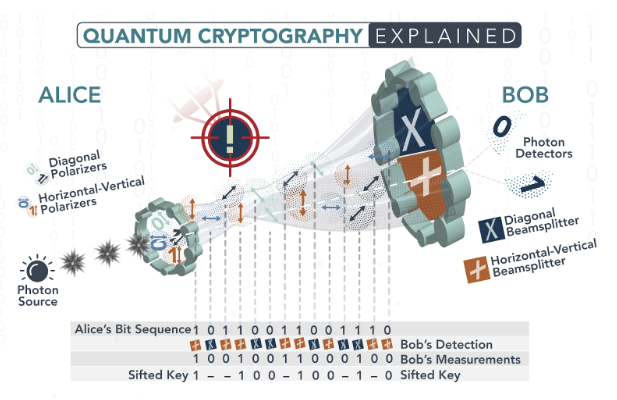
Exploring Quantum Cryptography: The Future of Unbreakable Encryption
June 14, 2023

Securing the Internet of Medical Things (IoMT)
June 17, 2023