Command injection vulnerabilities are a type of security vulnerability that allows an attacker to execute arbitrary commands on the underlying operating system of a web application. This can be done by injecting malicious code into a web application's input fields, such as a form field or a search query.
Once the malicious code is injected, the attacker can then execute arbitrary commands on the operating system. This can include commands that steal sensitive data, such as passwords or credit card numbers, or commands that can be used to take control of the web application server.
How Command Injection Vulnerabilities Work
Command injection vulnerabilities typically occur when a web application fails to properly sanitize user input. This can happen when the application passes user input directly to a system command without first validating it.
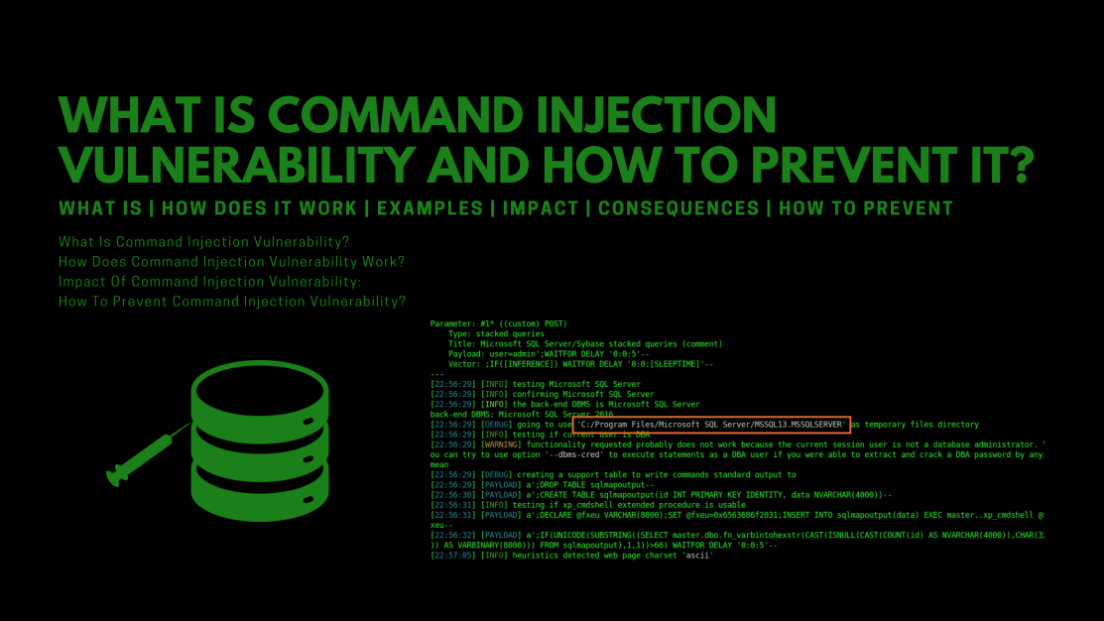
For example, a web application might have a form that allows users to search for files on the server. If the application fails to sanitize the user input, an attacker could inject malicious code into the search field. This code would then be executed by the system command when the user submits the search request.
The malicious code could be anything from a simple echo command that prints the contents of a file to a more complex script that steals passwords or takes control of the server. The possibilities are endless, and that's what makes command injection vulnerabilities so dangerous.
Mitigating Command Injection Vulnerabilities
There are a number of steps that can be taken to mitigate command injection vulnerabilities. These include:
Sanitizing user input: All user input should be sanitized before it is passed to a system command. This can be done by using a regular expression to filter out any malicious characters.
Using prepared statements: Prepared statements can be used to prevent command injection vulnerabilities. Prepared statements are a way of pre-compiling a SQL query, which helps to prevent SQL injection attacks.
Using input validation: Input validation can be used to check user input for malicious characters. This can be done by using a regular expression to filter out any malicious characters.
Examples of Command Injection Attacks
Here are some examples of command injection attacks:
File inclusion: An attacker could inject a malicious code that includes a file from the server's file system. This could be used to steal sensitive files, such as passwords or credit card numbers.
Remote command execution: An attacker could inject a malicious code that executes a command on the server's operating system. This could be used to take control of the server or to steal sensitive data.
Cross-site scripting (XSS): An attacker could inject a malicious code that is executed by the victim's browser. This could be used to steal cookies or to redirect the victim to a malicious website.
How to Prevent Command Injection Attacks
There are a number of ways to prevent command injection attacks. These include:
Sanitizing user input: All user input should be sanitized before it is passed to a system command. This can be done by using a regular expression to filter out any malicious characters.
Using prepared statements: Prepared statements can be used to prevent command injection vulnerabilities. Prepared statements are a way of pre-compiling a SQL query, which helps to prevent SQL injection attacks.
Using input validation: Input validation can be used to check user input for malicious characters. This can be done by using a regular expression to filter out any malicious characters.
Keeping software up to date: Software vendors often release security patches to fix known vulnerabilities. It is important to keep software up to date to help prevent command injection attacks.
Conclusion
Command injection vulnerabilities are a serious security threat that can be exploited by attackers to gain control of a web application server. There are a number of steps that can be taken to mitigate command injection vulnerabilities, such as sanitizing user input, using prepared statements, and using input validation.
By following these steps, web application developers can help to protect their applications from command injection attacks.