Mobile application penetration testing is a process of testing mobile apps to detect and identify loopholes or vulnerabilities before they are exploited for malicious gain to analyze the severity posed by them to the application through manual or automated penetration testing.
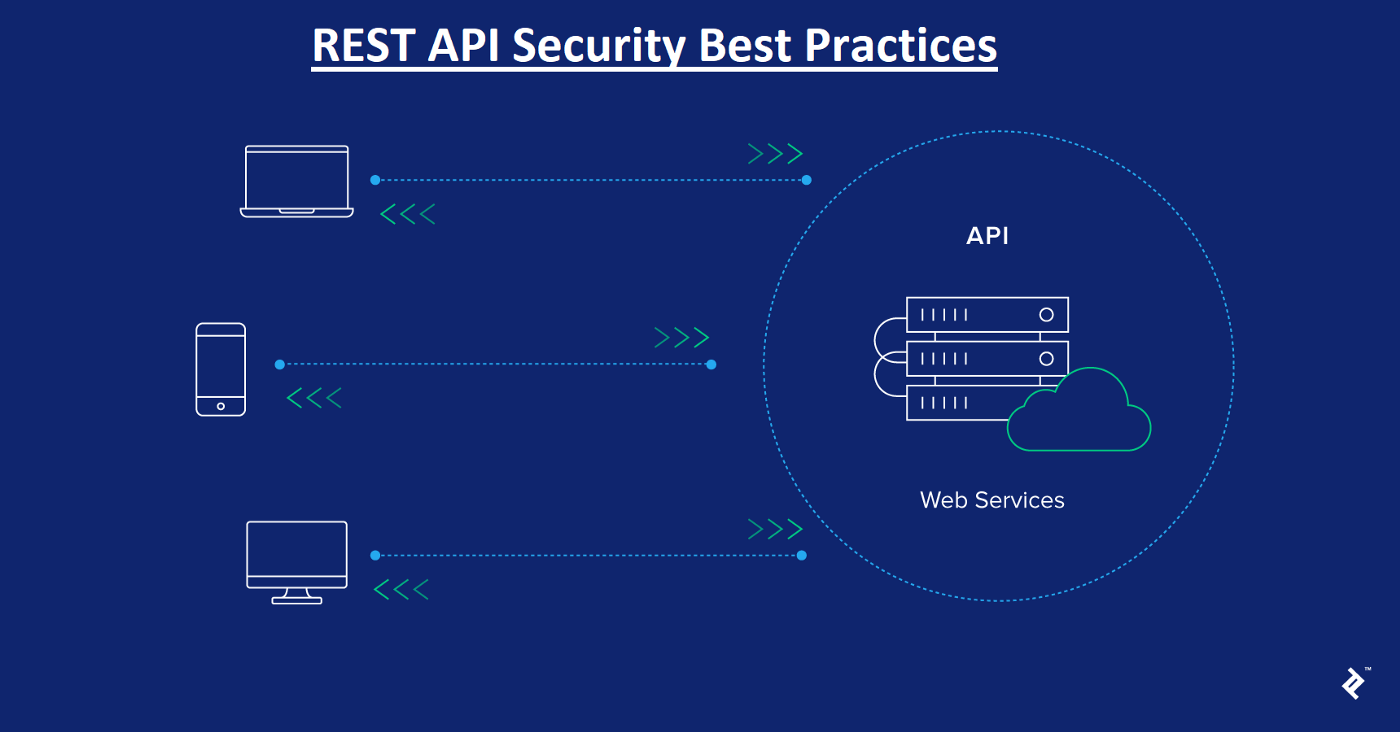
Web API exploitation is a type of attack that targets the web APIs that mobile apps use to communicate with back-end systems. Web APIs are often vulnerable to a variety of attacks, such as:
SQL injection: This attack involves injecting malicious SQL code into a web API request. This can be used to gain unauthorized access to the back-end database or to execute arbitrary commands on the server.
Cross-site scripting (XSS): This attack involves injecting malicious JavaScript code into a web API request. This can be used to steal cookies or session tokens, or to redirect users to malicious websites.
Insecure direct object reference: This vulnerability occurs when a web API allows access to resources without proper authorization. This can be exploited to access sensitive data or to modify data.
API key abuse: This attack involves using stolen or leaked API keys to access a web API without authorization. This can be used to steal data or to perform unauthorized actions.
Mobile application penetration testers can exploit web API vulnerabilities to gain unauthorized access to mobile apps, steal data, or perform unauthorized actions. By understanding the risks associated with web API exploitation, mobile application penetration testers can help organizations protect their mobile apps from attack.
Here are some additional tips for preventing web API exploitation in mobile apps:
Use a secure development lifecycle: The secure development lifecycle (SDLC) is a process that helps organizations develop secure software. The SDLC includes steps such as threat modeling, code review, and penetration testing.
Use a web application firewall (WAF): A WAF is a security appliance that can help protect web APIs from attack. WAFs can filter malicious traffic and block attacks.
Use a mobile app security testing tool: There are a number of mobile app security testing tools available that can help organizations identify and fix web API vulnerabilities.
By following these tips, organizations can help prevent web API exploitation in mobile apps and protect their sensitive data.
Conclusion
Web API exploitation is a serious threat to mobile apps. By understanding the risks associated with web API exploitation and taking steps to prevent it, organizations can help protect their mobile apps from attack.
Additional considerations
In addition to the tips outlined above, there are a few other considerations that should be taken into account when preventing web API exploitation in mobile apps. These include:
The type of mobile app: The type of mobile app will have a significant impact on the risks associated with web API exploitation. For example, a mobile app that stores sensitive data will be more vulnerable to attack than a mobile app that does not store sensitive data.
The target audience: The target audience for the mobile app will also have an impact on the risks associated with web API exploitation. For example, a mobile app that is targeted at children will be more vulnerable to attack than a mobile app that is targeted at adults.
The security posture of the organization; The security posture of the organization will also have an impact on the risks associated with web API exploitation. For example, an organization that has a strong security posture will be less vulnerable to attack than an organization that has a weak security posture.
By taking these considerations into account, organizations can help prevent web API exploitation in mobile apps and protect their sensitive data.