Web Penetration Testing - Sql Injection
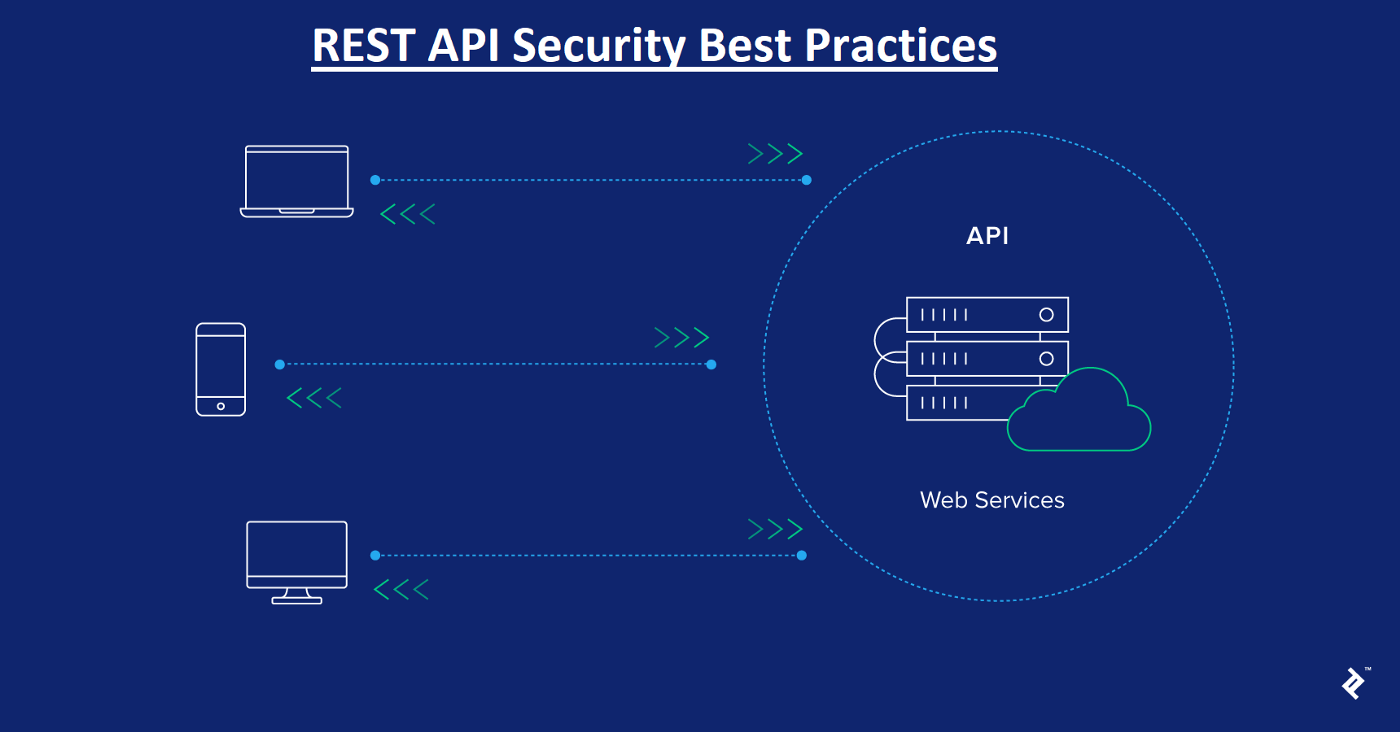
Security Considerations for RESTful Web Services
July 31, 2023

GraphQL Security: Common Vulnerabilities and Best Practices
July 25, 2023

Zero-Day Vulnerabilities: Web Application Exploitation
June 21, 2023

Secure Coding Practices for Web Developers
July 20, 2023

Mobile Application Penetration Testing: Web API Exploitation
July 14, 2023
Anatomy of a Web Penetration Test: Step-by-Step Process
July 14, 2023
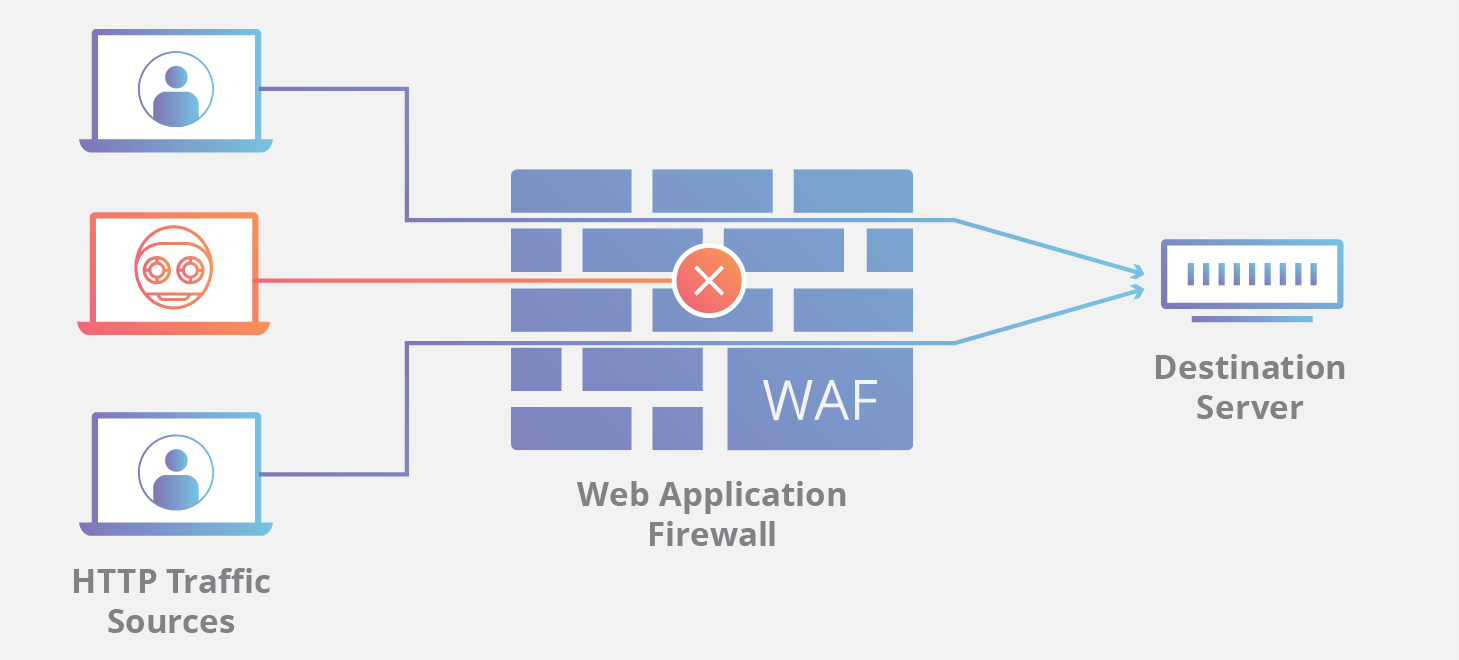
Web Application Firewalls (WAFs): How They Work and Their Limitations
July 8, 2023

Exploring SQL Injection Attacks in Web Applications
July 5, 2023

Common Web Application Vulnerabilities and Exploits
July 4, 2023

CVE-2022-34265 Exploit Step-by-Step
June 9, 2023