Web Penetration Testing - Testing

Web Application Reconnaissance Techniques for Penetration Testing
July 29, 2023

Assessing Third-Party Web Application Security Risks
July 28, 2023

DOM-Based XSS Attacks: Detection and Prevention
July 27, 2023
Business Logic Flaws in Web Applications: Detection and Exploitation
July 24, 2023
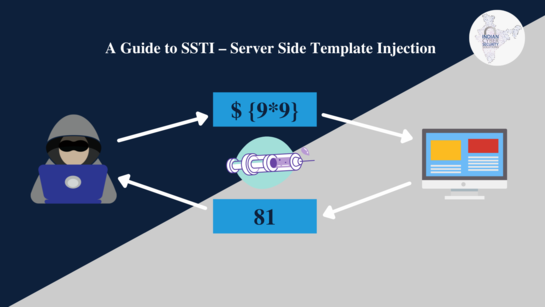
Server-Side Template Injection (SSTI): Exploitation Techniques
July 15, 2023

Mobile Application Penetration Testing: Web API Exploitation
July 14, 2023
Anatomy of a Web Penetration Test: Step-by-Step Process
July 14, 2023
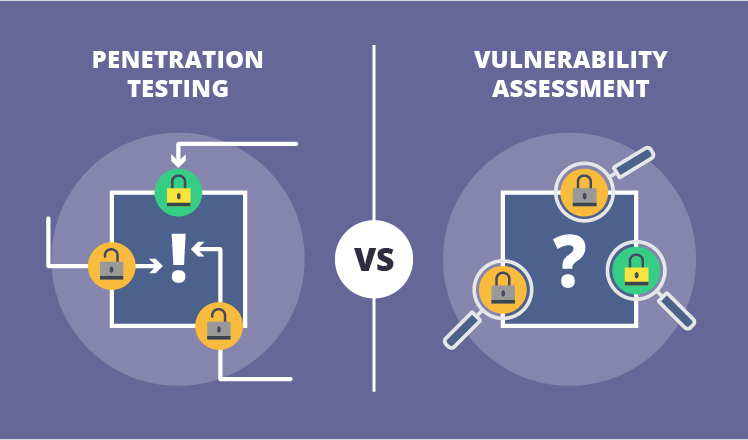
Vulnerability Assessment vs. Penetration Testing: What's the Difference?
July 13, 2023

Web Application Security Scanning Tools: A Comparative Analysis
July 12, 2023
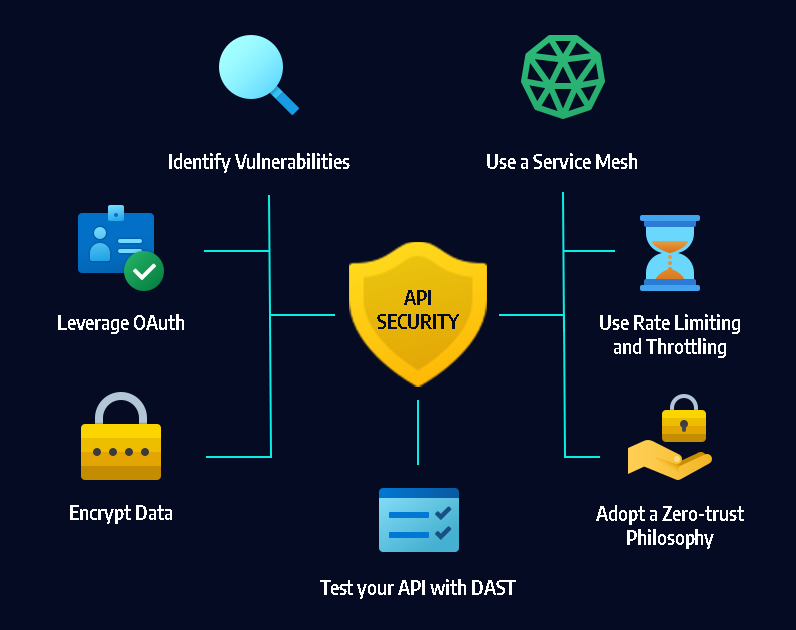
API Security Testing: Best Practices and Tools
July 12, 2023

Penetration Testing and Reporting Results Effectively
May 12, 2023

Protecting Your Wireless Network Against Cyber Attacks
May 12, 2023

Assessing the Security of Cloud Environments
May 13, 2023

Best ways to learn web penetration testing, ethical hacking, and IT security
July 4, 2023
Network Penetration Testing For Weaknesses
May 11, 2023

Automating Metasploit with Pymetasploit3 in Continuous Integration
May 8, 2023

How to Develop a Cybersecurity Incident Response Plan for Your Business
May 6, 2023

Understanding Different Web Application Security Testing Techniques
June 5, 2023

Advantages And Disadvantages Of Penetration Testing
June 6, 2023
What Technique is Used To Automate The Detection Of Web Application Vulnerabilities
May 30, 2023
Web Penetration Testing In Agile Development Environments
May 31, 2023

How Can We Automate Penetration Testing In Order To Improve Network Security
June 2, 2023