Web Penetration Testing - Attack

WebSocket Hijacking: Techniques and Countermeasures
July 31, 2023

Cryptographic Weaknesses in Web Applications: Attacks and Fixes
July 26, 2023

GraphQL Security: Common Vulnerabilities and Best Practices
July 25, 2023
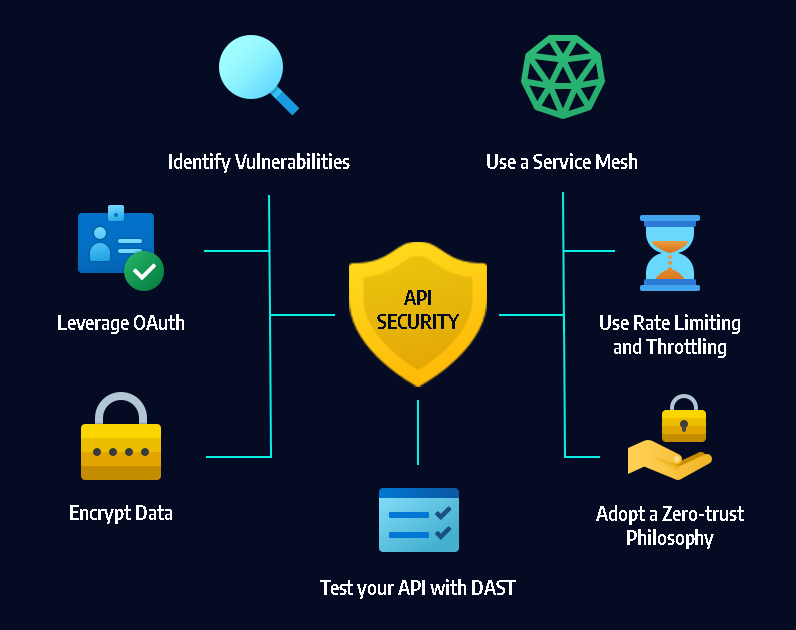
API Token Security: Risks and Recommendations
July 25, 2023
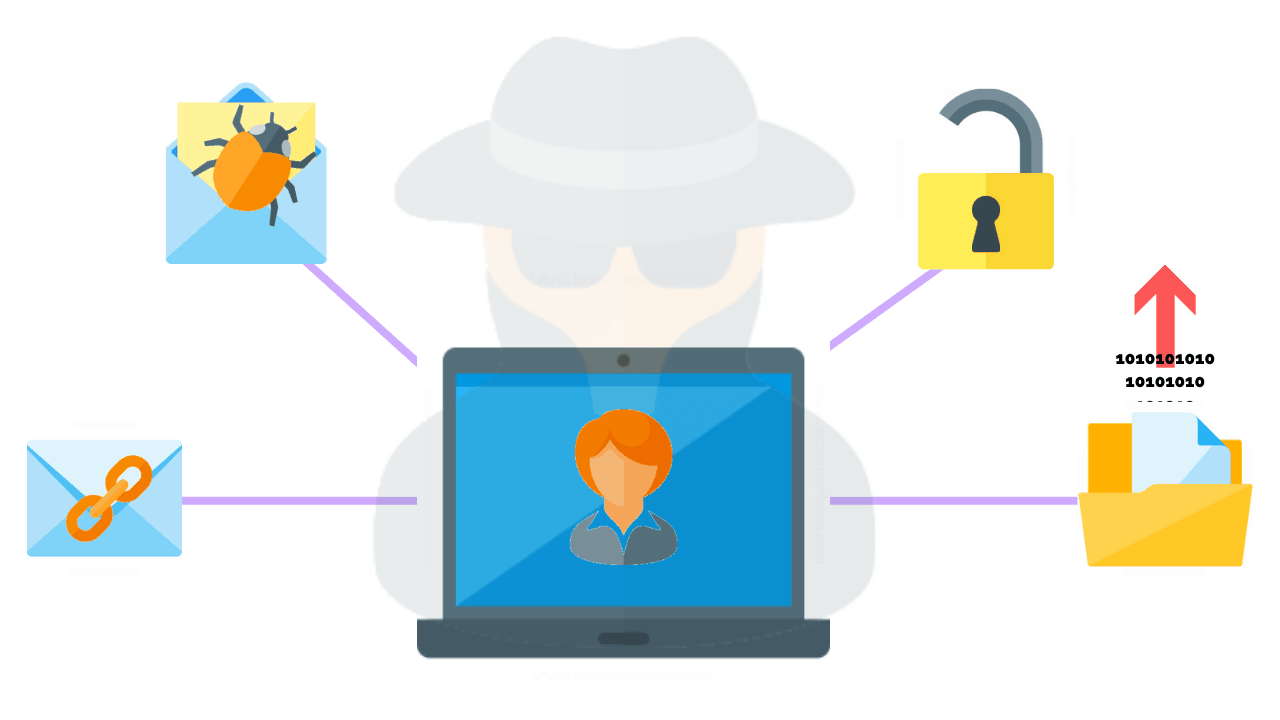
Social Engineering Techniques in Web Penetration Testing
July 22, 2023
Importance of Secure Session Management in Web Applications
July 22, 2023

Biometric Authentication: Security Challenges in Web Applications
July 21, 2023
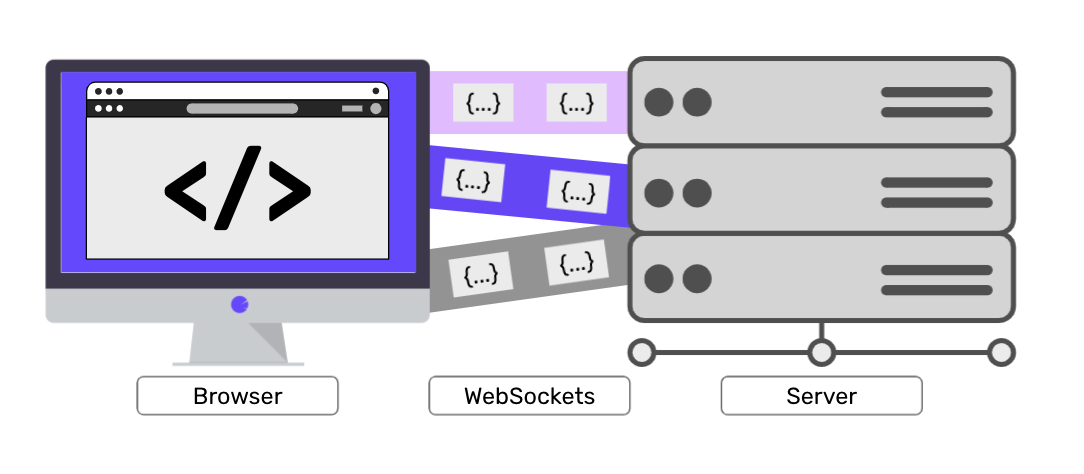
Websockets Security: Threats and Countermeasures
July 20, 2023

Clickjacking Attacks: Techniques and Mitigation
July 19, 2023
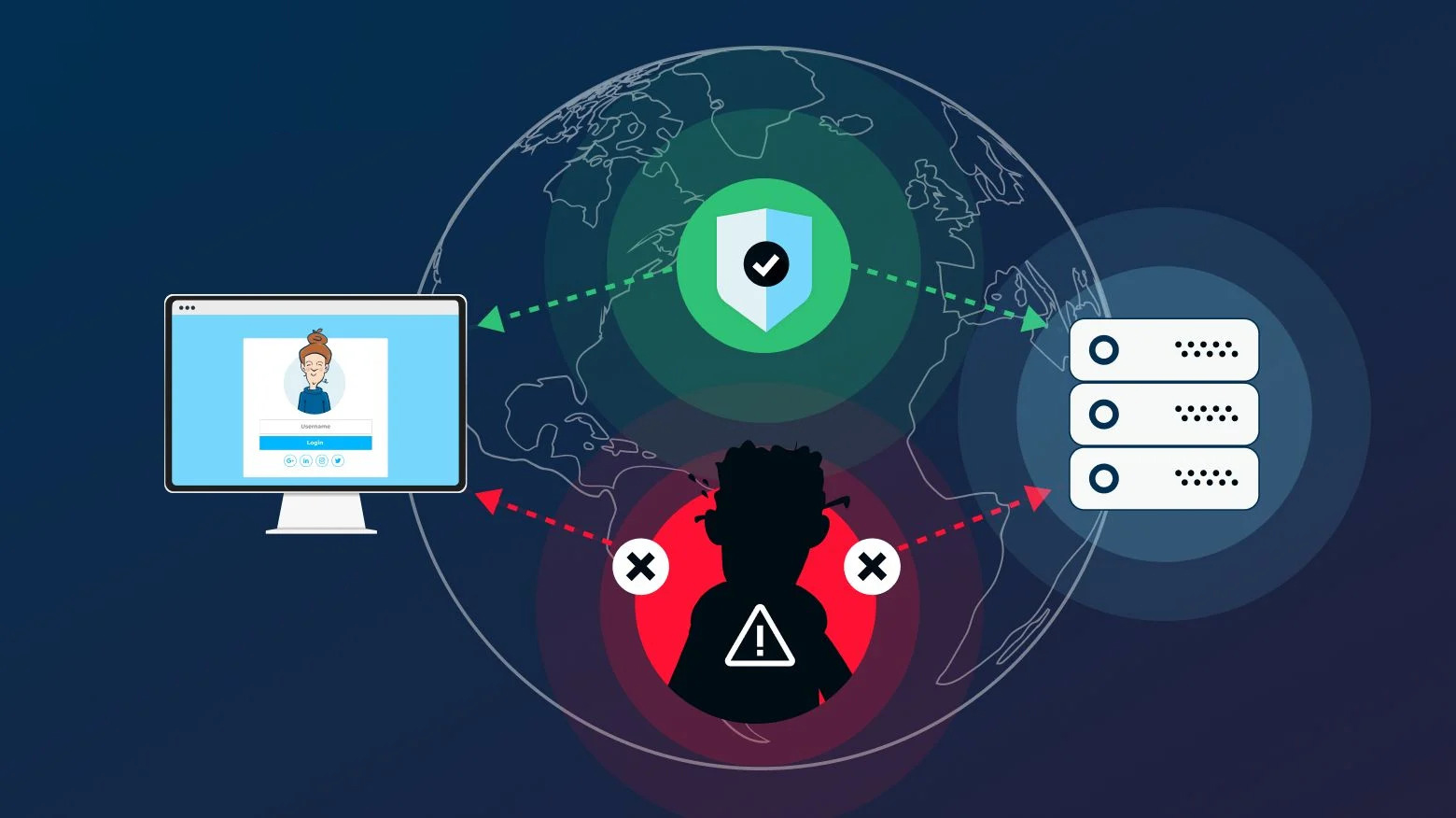
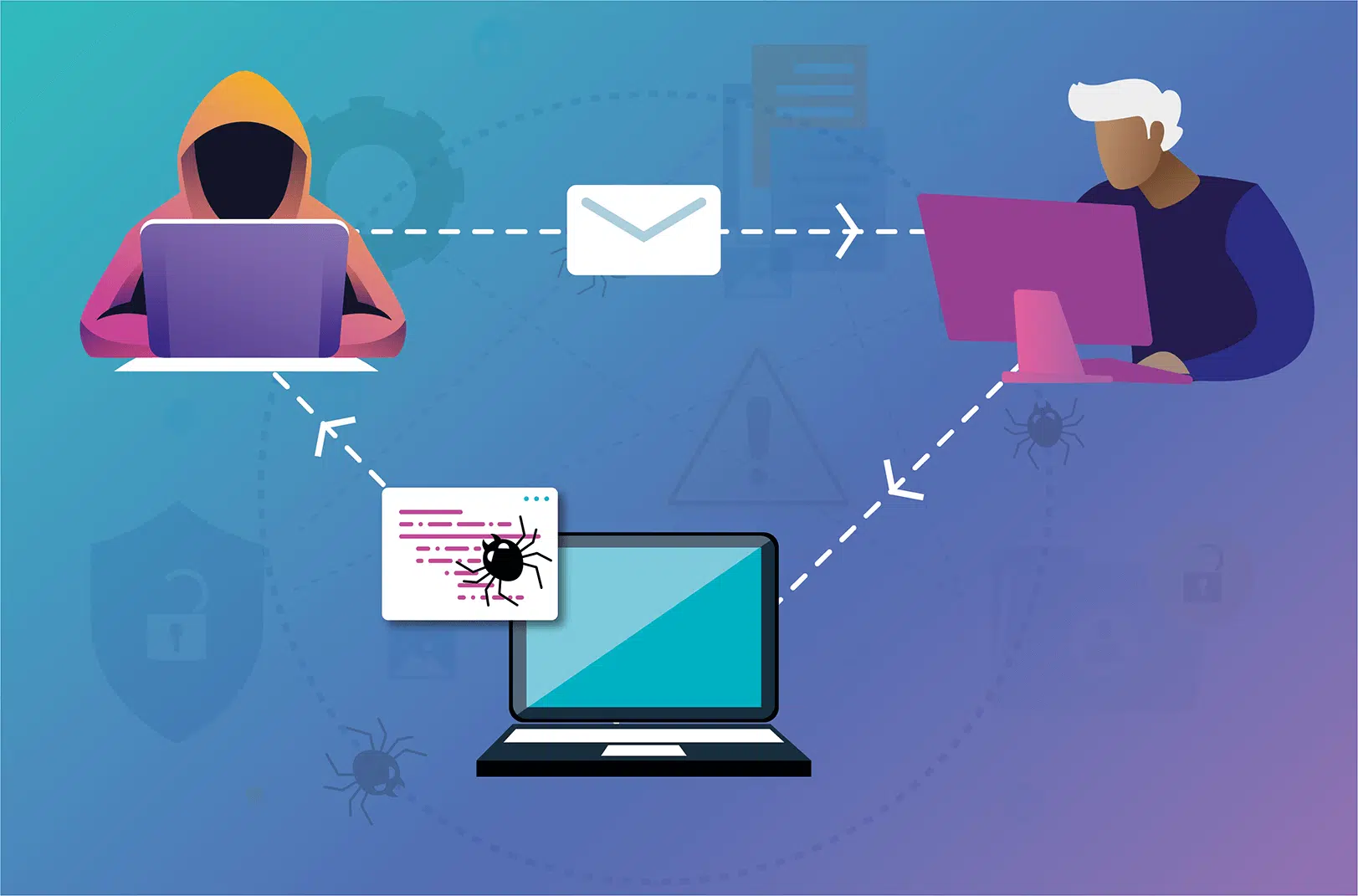
Man-in-the-Middle (MitM) Attacks on Web Applications
July 18, 2023
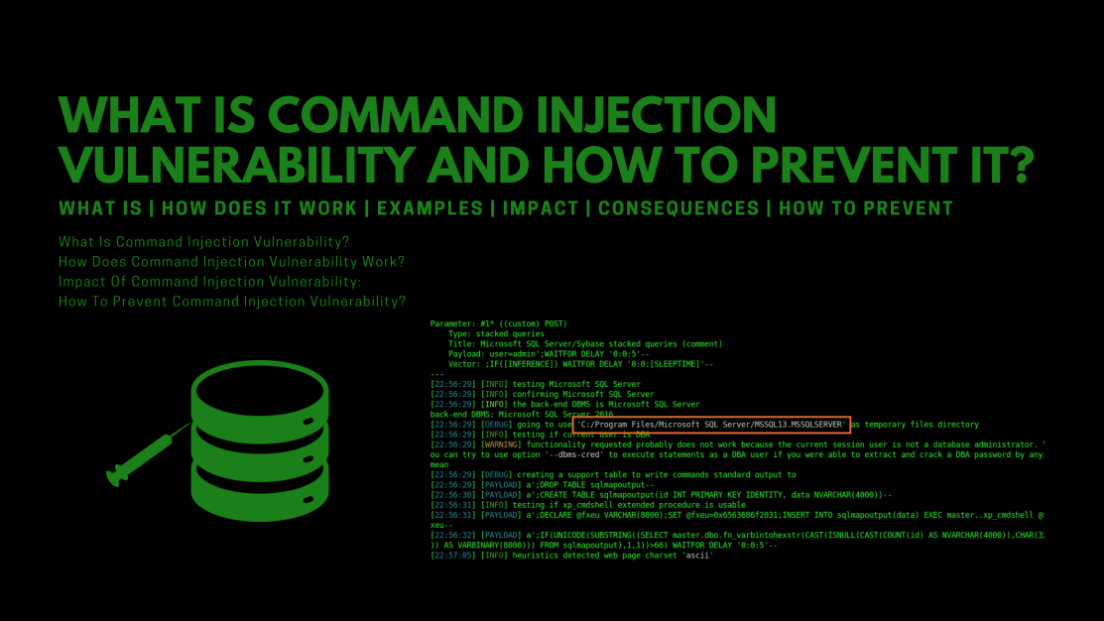
Exploiting Command Injection Vulnerabilities in Web Applications
July 15, 2023

Remote File Inclusion (RFI) and Local File Inclusion (LFI) Attacks
July 11, 2023
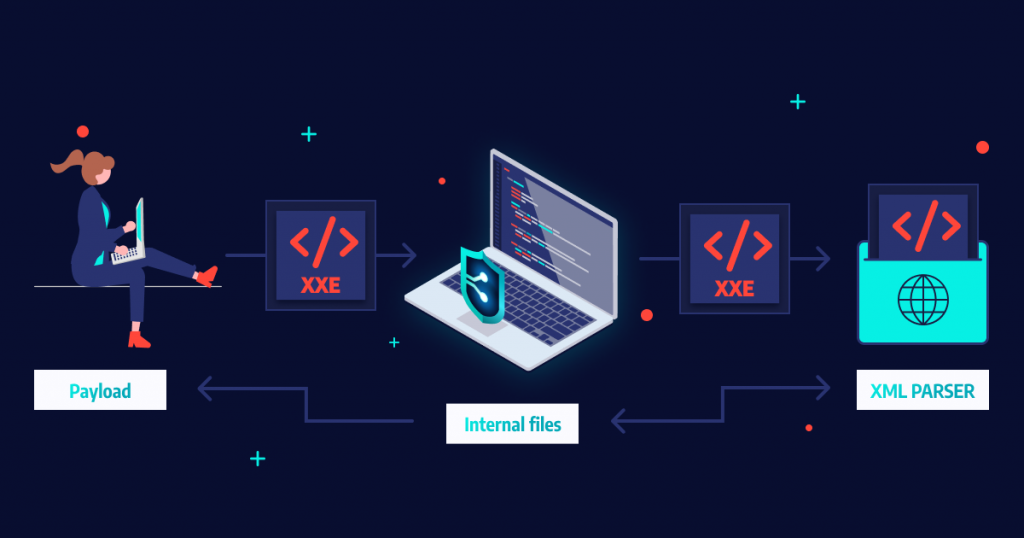
XML External Entity (XXE) Attacks
July 11, 2023

Brute Force Attacks: Methods and Prevention in Web Applications
July 10, 2023
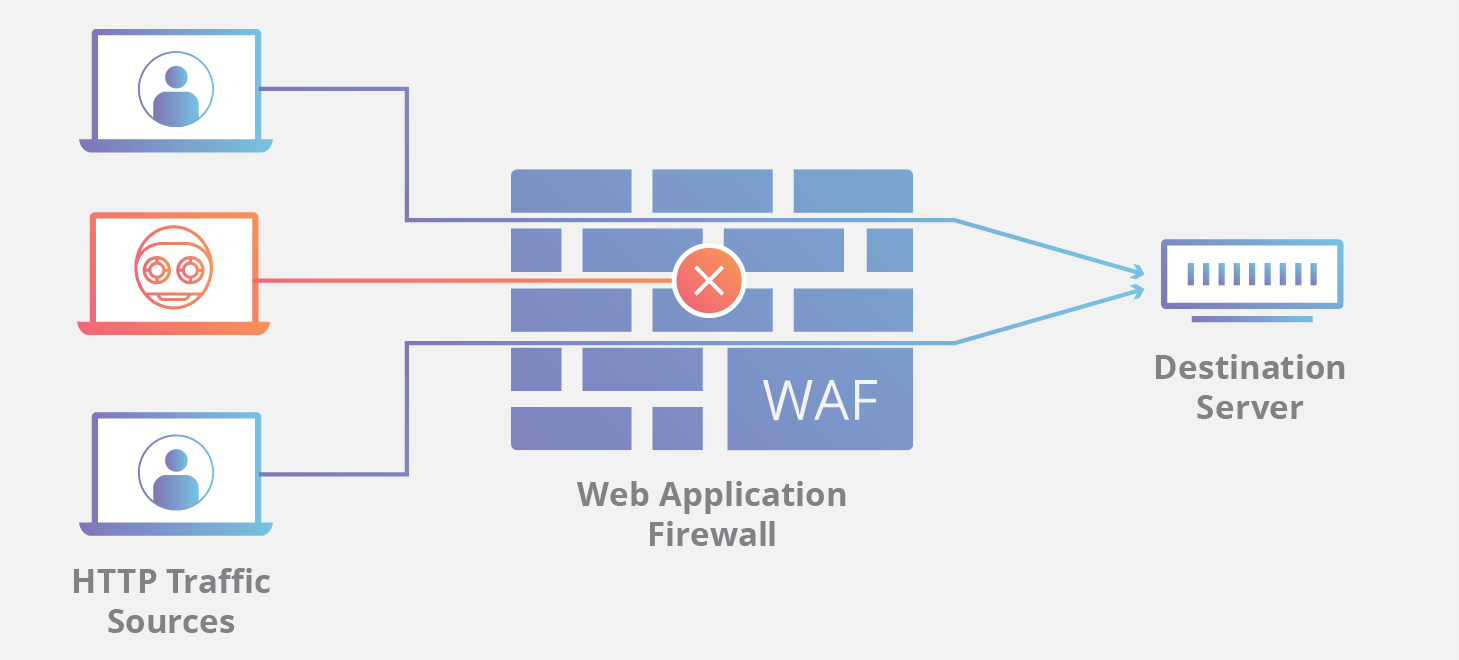
Web Application Firewalls (WAFs): How They Work and Their Limitations
July 8, 2023

Directory Traversal Attack Case Study
July 7, 2023
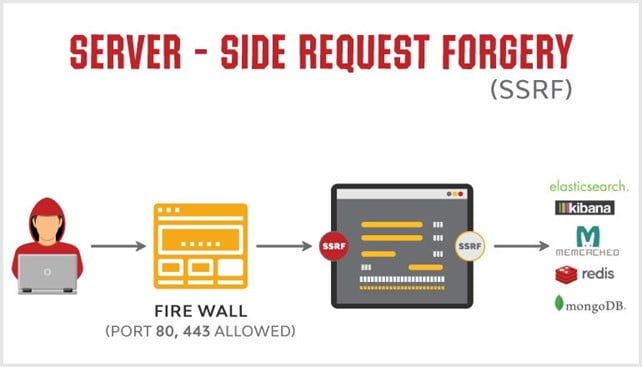
What is a Server-Side Request Forgery (SSRF) and how can they be prevented?
July 6, 2023

Cross-Site Scripting (XSS) Attacks: Techniques and Prevention
July 6, 2023
What is a cross-site scripting (XSS) attack? What is the purpose of attackers?
July 5, 2023

Exploring SQL Injection Attacks in Web Applications
July 5, 2023

Ransomware Mitigation Strategies
May 12, 2023

Protecting Your Wireless Network Against Cyber Attacks
May 12, 2023

Assessing the Security of Cloud Environments
May 13, 2023

Collecting Volatile Data and Identifying Attack Patterns through Forensic Analysis
May 15, 2023

US Government Data Breach Exposes Personal Information of Employees
May 17, 2023

MSI Data Breach Exposes Customer Data
May 18, 2023

Atlassian Data Breach: What You Need to Know
May 20, 2023

Activision Data Breach
May 20, 2023
PayPal Data Breach: What You Need to Know
May 22, 2023

MailChimp Breach Exposes Data of 133 Customers
May 23, 2023

Twitter Data Breach
May 24, 2023

American Airlines Data Breach: What You Need to Know
May 26, 2023

AirAsia Data Breach: What You Need to Know
May 27, 2023

Medibank Data Breach
May 29, 2023
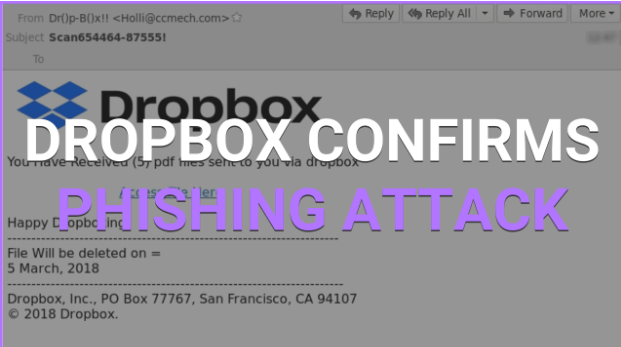
Dropbox Data Breach: What You Need to Know
May 30, 2023

Common Web Application Vulnerabilities and Exploits
July 4, 2023

Rising Threat of Ransomware and its Prevention By AI and Machine Learning
May 11, 2023

The Future of Ransomware
May 11, 2023

Ransomware and the Supply Chain
May 10, 2023

Top Cybersecurity threats facing businesses in 2023
May 9, 2023

JBS Foods Ransomware Attack: Everything You Need To Know
May 8, 2023

Understanding the Psychology of Cybercriminals
May 5, 2023

Understanding the Importance of Cyber Insurance in Today's Business
May 6, 2023

The NotPetya Ransomware Attack: A Case Study in Destructive Malware
May 8, 2023

How to Develop a Cybersecurity Incident Response Plan for Your Business
May 6, 2023

Role of AI in Cybersecurity: Opportunities & Challenges
May 5, 2023

Advantages And Disadvantages Of Penetration Testing
June 6, 2023
What Technique is Used To Automate The Detection Of Web Application Vulnerabilities
May 30, 2023

Threat Modelling For Web Penetration Testing: Assessing Risks And Impact
June 1, 2023

What Type Of Web Application Vulnerabilities Are Humans Typically Better At Discovering
June 9, 2023

The Latest Ransomware Attacks and How to Avoid Them
June 10, 2023